Secure KVM switches are designed from the ground up as dedicated switching devices with every element conceived to prevent unauthorized access and ensure data isolation. The design of Secure KVM switches is optimized for use in accessing networks at different levels of security, including government, military, and defense operations.

Having isolation between a Secure Network and a Non-Secure Network allows the user to access both systems from one user station thus saving space and costs.
Modern government agencies and defense departments are increasingly reliant on electronic systems. Electronic emissions may pose a threat to secure environments as these emissions provide a conduit by which sensitive information could easily leak into the wrong hands. Video cables, for example, can emit strong emissions that can be collected and duplicated to view the same image elsewhere. Another threat includes power sources that can be used to conduct data back into a mains electricity supply and this in turn can be picked out using sensitive devices outside of the system's physical location. Typical KVM switches that do not actively combat these leakage threats may therefore pose a significant security risk.
Secure KVM Requirements & Features
Isolated Data Channels
Isolated Data Channels in each KVM port make it impossible for data to be transferred between connected computers through the KVM.
'No-Buffer' Design
Secure KVMs do not utilize a physical memory buffer, thus preventing any eavesdropping or key logging attempts. The keyboard and mouse USB buffers are automatically cleared after data transmission.
Housing Intrusion Detection
Housing Intrusion Detection causes the KVM system to become inoperable and the LEDs to flash repeatedly if the housing has been opened.
Locked Firmware
Locked Firmware prevents any attempts to alter the operation of the KVM.
Tamper-Proof Circuit Board
Tamper-Proof Circuit Board is soldered to prevent component removal or alteration.
Tamper-Proof Labels
Tamper-Proof Labels on the KVM chassis provide clear visual evidence if the enclosure has been opened or compromised.
Restricted USB function
Restricted USB function only recognizes USB keyboards and mice to prevent inadvertent and insecure data transfer. Other USB devices, such as USB storage drives, are actively prohibited.
Push-Button Control
Push-Button Control requires physical access to KVM when switching between connected computers. Keyboard "Hot Key" shortcuts, automatic scanning, voice activation, and other switching methods requiring buffer are prohibited.
CC Protection Profiles for KVM Switches
Common Criteria (CC) evaluates KVM (Keyboard-Video-Mouse) switches, KM (Keyboard-Mouse) switches, KVM splitters (Reverse KVMs), and Multi-viewers using the Protection Profile for Peripheral Sharing Switches. NOTE the Peripheral Sharing Protection Profile is not suitable for the evaluation against over-IP, network-attached switches, and matrix switches.
There are two main versions of the PPS that are commonly used in modern Secure KVM switches:
- Protection Profile for Peripheral Sharing Switch Version 3.0
- Protection Profile for Peripheral Sharing Switch Version 2.1
Protection Profile Version 3.0: The new NIAP Version 3.0 Protection Profile for Peripheral Sharing Switches defines the latest requirements for use of Secure Desktop KVM Switches. Compliance with Protection Profile for Peripheral Sharing Switches version 3.0 ensures peripheral sharing capabilities provide maximum user data security when switching port focus, preventing unauthorized data flows or leakage between connected sources.
NOTE The new 3.0 Protection Profile (PP_PSS_V3.0) replaces the previous EAL2, EAL4 and Common Criteria regulations with stricter requirements.
Common Criteria Evaluation & Certification
"By awarding a Common Criteria certificate, the CC Certification Body (CCS) asserts that the product complies with the security requirements specified in the associated security target. A security target is a requirements specification document that defines the scope of the evaluation activities. The consumer of certified IT products should review the security target, in addition to this certification report, in order to gain an understanding of any assumptions made during the evaluation, the IT product's intended environment, its security requirements, and the level of confidence (i.e., the evaluation assurance level) that the product satisfies the security requirements." - Common Criteria(2)
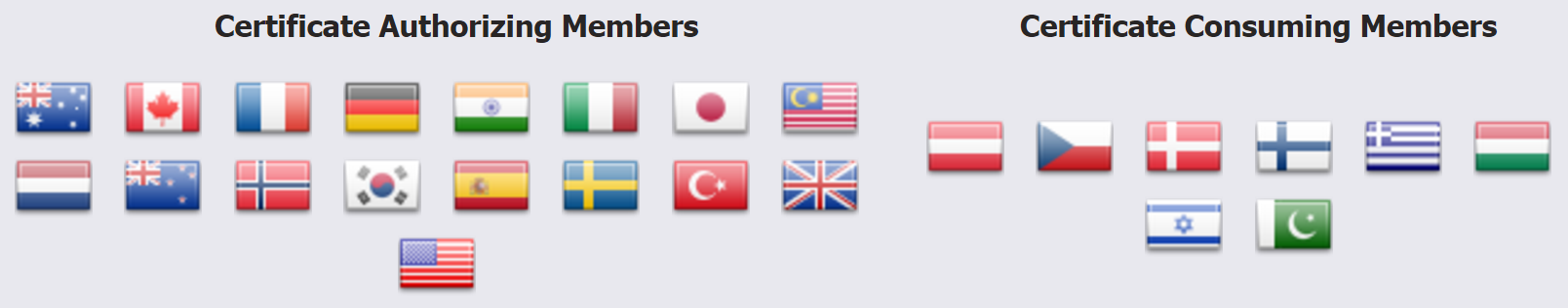
Photo courtesy of https://www.commoncriteriaportal.org/ccra/members/
The international Common Criteria Recognition Arrangement (CCRA) brings together 26 nations whom agreed to accept a unified approach to the evaluations of IT product information assurance and security. Evaluations in the United States are performed by a commercial Common Criteria (CC) testing laboratory under the oversight of the National Information Assurance Partnership (NIAP) - a collaboration between Nation Institute of Standards and Technology (NIST) and the National Security Agency (NSA).
What are EAL 2 & EAL 4?
An Evaluation Assurance Level (EAL) is a security rank assigned to an IT product or system after a Common Criteria (CC) security evaluation. The level indicates to what extent the product or system was tested. NOTE A higher EAL rating does not indicate a higher level of security.
A product or system must meet specific assurance requirements to achieve a particular EAL. Requirements involve design documentation, analysis and functional or penetration testing. The highest numerical level provides the highest guarantee that the system's principal security features are reliably applied and tested.
EAL 2: Structurally Tested. Analysis of the security functions using a functional and interface specification and the high level design of the subsystems of the TOE. Independent testing of the security functions, evidence of developer "black box" testing, and evidence of a development search for obvious vulnerabilities.
- Shop Secure KVM Switches with EAL 2
EAL 4: Methodically Designed, Tested and Reviewed. Analysis is supported by the low-level design of the modules of the TOE, and a subset of the implementation. Testing is supported by an independent search for obvious vulnerabilities. Development controls are supported by a life-cycle model, identification of tools, and automated configuration management. - National Technical Authority for Information Assurance(5)
What is the TEMPEST Certification?
TEMPEST is a specification created by NSA and NATO for certifying IT systems against the possibility of spying through leaking emanations such as electrical signals, radio waves, sounds, and vibration. While most of TEMPEST covers electrical signal and radio wave emanation, it also stringently covers sound and mechanical vibration. "For example, it is possible to log a user's keystrokes using the motion sensor inside smartphones." (4)
Many specifics of the TEMPEST standards are classified and therefore not available for public review; however, protecting equipment from eavesdropping is achieved by shielding, filtering, masking, and limiting the distance of transmissions. TEMPEST covers the entire IT system, not individual components of the system.
There are three standard levels of TEMPEST protection:
- Level 1 is the most strict standard where it is assumed that the attacker could gain physical access to the device.
- Level 2 and 3 are more relaxed assuming the attacker could get within 20 meters (65 feet) or 100 meters (330 feet) respectively.
Questions About Secure KVMs? We're Here to Help!
References:
- (1) National Information Assurance Partnership (NIAP)
- (2) The Common Criteria (CC)
- (3) Adder - "Tempest and EAL4+ qualified secure KVM switches launched"
- (4) Wikipedia - "Tempest (codename)"
- (5) National Technical Authority for Information Assurance - CC Assurance Levels
Other Resources:
- 42U Data Center Solutions - Secure KVM Switches
- NIAP-CCEVS - Documents and Guidance






